[ad_1]
Microsoft has introduced the seizure of dozens of domains utilized in assaults by the China-based APT group Nickel on governments and NGOs throughout Europe, the Americas and the Caribbean.
In two weblog posts printed on Monday, Microsoft vp Tom Burt, the Microsoft Digital Crimes Unit and the Microsoft Risk Intelligence Heart stated they’ve been monitoring Nickel since 2016 and {that a} federal courtroom in Virginia granted the corporate’s request to grab web sites the group was utilizing to assault organizations within the US and and different nations.
Burt defined that on December 2, the corporate filed lawsuits within the US District Courtroom for the Japanese District of Virginia that may permit them to “reduce off Nickel’s entry to its victims and stop the web sites from getting used to execute assaults.”
“We imagine these assaults have been largely getting used for intelligence gathering from authorities companies, suppose tanks and human rights organizations,” Burt stated.
“The courtroom shortly granted an order that was unsealed in the present day following completion of service on the internet hosting suppliers. Acquiring management of the malicious web sites and redirecting visitors from these websites to Microsoft’s safe servers will assist us shield present and future victims whereas studying extra about Nickel’s actions. Our disruption won’t forestall Nickel from persevering with different hacking actions, however we do imagine now we have eliminated a key piece of the infrastructure the group has been counting on for this newest wave of assaults.”
Microsoft
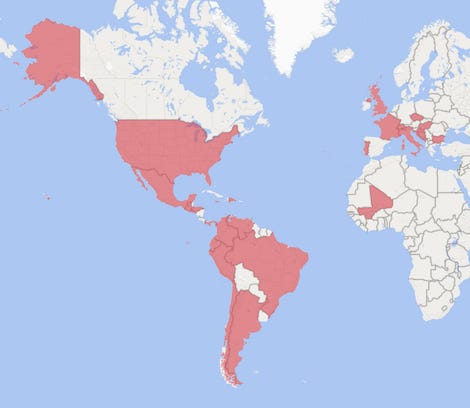
The assaults — which concerned inserting hard-to-detect malware that enabled intrusions, surveillance and information theft — focused organizations in Argentina, Barbados, Bosnia and Herzegovina, Brazil, Bulgaria, Chile, Colombia, Croatia, Czech Republic, Dominican Republic, Ecuador, El Salvador, France, Guatemala, Honduras, Hungary, Italy, Jamaica, Mali, Mexico, Montenegro, Panama, Peru, Portugal, Switzerland, Trinidad and Tobago, the UK, US and Venezuela.
The Microsoft Risk Intelligence Heart discovered that typically, Nickel was capable of compromise VPN suppliers or get hold of stolen credentials whereas in different situations, they took benefit of unpatched Change Server and SharePoint programs.
The corporate famous that no new vulnerabilities in Microsoft merchandise have been used as a part of the assaults. However as soon as attackers have been within a community, they regarded for tactics to realize entry to higher-value accounts or different footholds within the system. Microsoft stated they noticed Nickel actors utilizing Mimikatz, WDigest, NTDSDump and different password dumping instruments throughout assaults.
“There’s typically a correlation between Nickel’s targets and China’s geopolitical pursuits. Others within the safety neighborhood who’ve researched this group of actors discuss with the group by different names, together with ‘KE3CHANG,’ ‘APT15,’ ‘Vixen Panda,’ ‘Royal APT’ and ‘Playful Dragon,'” Burt defined.
“Nation-state assaults proceed to proliferate in quantity and class. Our purpose on this case, as in our earlier disruptions that focused Barium, working from China, Strontium, working from Russia, Phosphorus, working from Iran, and Thallium, working from North Korea, is to take down malicious infrastructure, higher perceive actor techniques, shield our prospects and inform the broader debate on acceptable norms in our on-line world.”
Burt added that up to now, Microsoft has filed 24 lawsuits that allowed them to take down greater than 10,000 malicious web sites from cybercriminals and virtually 600 from nation-state teams.
Jake Williams, CTO of BreachQuest, famous that the methods utilized by Nickel after preliminary entry are pretty pedestrian, whereas lots of the different instruments are available and extensively utilized by penetration testers.
“Whereas NICKEL actually has entry to instruments which might be way more succesful, they flip again to those commonplace instruments as a result of they work,” Williams stated. “That these available instruments can function in any respect speaks to the extent of safety in goal networks.”
[ad_2]
Source link









