[ad_1]
It has been a busy week for hacking and extortion collective Lapsus$. It first leaked what it claimed to be worker account info from LG Electronics, in addition to supply code for a wide range of Microsoft merchandise.
A number of hours later, the group additionally launched screenshots indicating it had breached identification and entry administration firm Okta. Information of the potential breach unfold rapidly on-line.
Okta gives a single sign-on service for giant organizations that permits workers to log in to a number of techniques with out requiring a unique password for every one. An Okta hack might have probably extreme implications for patrons.
Okta’s response
Okta revealed a preliminary assertion on Tuesday morning, indicating that the screenshots Lapsus$ launched got here from “an try to compromise the account of a 3rd get together buyer assist engineer working for one in all our subprocessors” that occurred in January this yr.
A second assertion from David Bradley, Chief Safety Officer at Okta, supplied extra particulars concerning the “unsuccessful try” to breach the assist engineer’s account.
Whereas reassuring prospects that “the Okta service has not been breached and stays totally operational”, he additionally admitted {that a} forensic investigation discovered “there was a five-day window of time between January 16-21, 2022, the place an attacker had entry to a assist engineer’s laptop computer”. Bradley insisted, nevertheless, that “[t]he potential impression to Okta prospects is restricted to the entry that assist engineers have”, noting particularly that the hacking group can not obtain buyer information and doesn’t have entry to passwords.
Unbiased safety researcher Invoice Demirkapi supplied additional particulars to TechRadar Professional by way of e-mail. He defined that the third-party assist engineer appeared to work for SYKES Enterprises, Inc, now confirmed by Okta, and that, “utilizing the entry this assist workers had, Lapsus$ was capable of breach Okta’s inner Slack, Jira, and backend administrative entry panel used to help prospects”. He added that, “presently, it doesn’t seem like Lapsus$ nonetheless has entry to Okta’s atmosphere.”
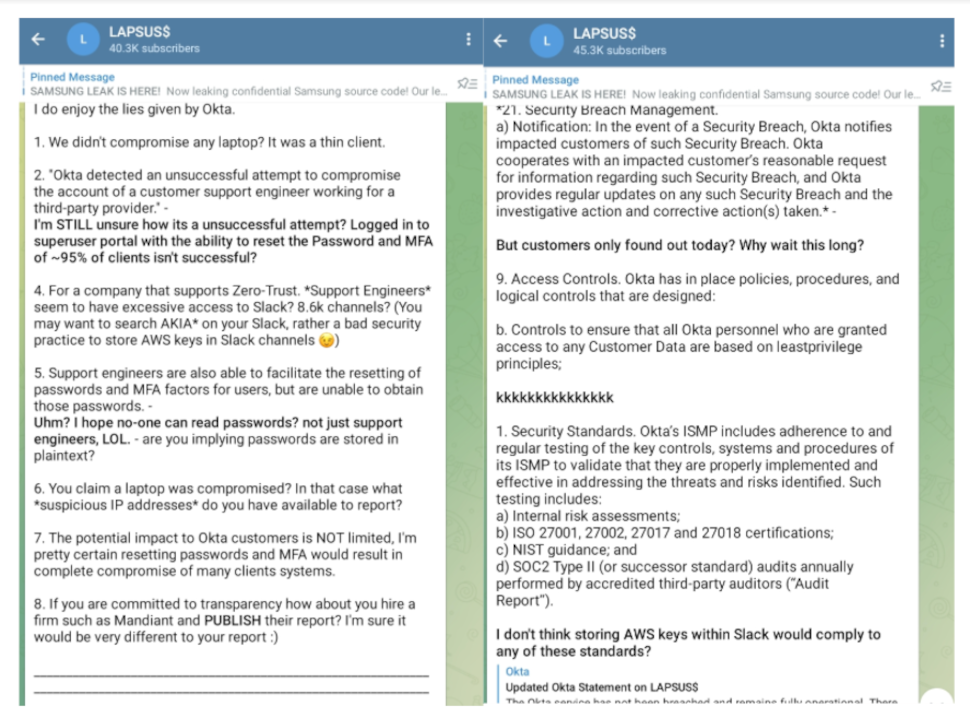
On Tuesday afternoon, Lapsus$ responded to Bradley’s assertion in its Telegram channel, taking challenge along with his characterization of the assault as “unsuccessful”. Lapsus$ additionally claimed that Okta had been storing AWS keys in Slack and known as the corporate out for ready so lengthy to inform their customers concerning the January incident.
Bradley has since acknowledged that “a small share of consumers – roughly 2.5% [366 companies] – have probably been impacted” by the incident and will have had their information “considered or acted upon”, although he continues to insist “there aren’t any corrective actions our prospects must take”.
In a separate submit, Bradley laid out a timeline for the incident and addressed Lapsus$’s earlier reference to a “superuser” portal, shutting down claims that this gave the group “god-like entry” to buyer accounts. As an alternative, Bradley clarified that the superuser portal “is an software constructed with least privilege in thoughts to make sure that assist engineers are granted solely the particular entry they require to carry out their roles”.
Okta has confronted criticism, each from Lapsus$ and the safety trade, for not disclosing the January incident sooner. Unsurprisingly, the breach has made buyers nervous, resulting in a drop in Okta’s inventory worth, in addition to a downgrade from Raymond James Fairness Analysis.
Who’s Lapsus$?
Regardless of the chaos its members prompted this week, Lapsus$ is comparatively new to the cybercrime scene. The hacking collective first emerged on the finish of final yr, however has already breached large names, together with Microsoft, Nvidia, Samsung and Ubisoft.
On Tuesday, Microsoft revealed a report about Lapsus$, noting the group is unconventional, as a result of it broadcasts its actions on social media and overtly recruits workers keen to offer them entry to firms they need to hack.
Whereas gaining the group on-line followers, Lapsus$’s social media presence additionally works to its detriment. Lapsus$ made the assault on Microsoft recognized on social media whereas it was going down, which Microsoft stated “escalated our motion permitting our workforce to intervene and interrupt the actor mid-operation, limiting broader impression”.
Bloomberg reported on Wednesday that two of Lapsus$’s members are regarded as youngsters, one dwelling close to Oxford within the UK and one in Brazil. The British teenager, recognized by the aliases “White” and “Breachbase”, was recognized by cybersecurity researchers as early as mid-2021 after leaving a path of details about himself on-line. He was additionally doxxed by different hackers, who declare he has practically $14 million in cryptocurrency.
On Thursday, the BBC reported that seven folks between the ages of 16 and 21 had been arrested by London police as a part of an investigation associated to Lapsus$, although it’s not clear whether or not the youngsters talked about by Bloomberg have been amongst these arrested. The seven have since been launched below investigation.
On Tuesday evening, Lapsus$ introduced that the group “could be quiet” for some time, since a few of their members have been happening “trip till 30/3/2022″. Whereas the group promised to “attempt to leak stuff ASAP”, in gentle of the current arrests, the collective could also be taking an extended break than meant.
Regardless of their youthfulness, the teenager members of Lapsus$ are extraordinarily educated. As Microsoft famous, Lapsus$ “understands the interconnected nature of identities and belief relationships in trendy know-how ecosystems and targets telecommunications, know-how, IT providers and assist firms to leverage their entry from one group to entry the accomplice or provider organizations”.
How firms can defend themselves
Microsoft’s report contained recommendation for firms about the best way to defend themselves towards assaults from Lapsus$. The report famous that “multifactor authentication (MFA) is likely one of the major traces of protection towards” the hacking collective. However it additionally emphasised that insecure strategies, equivalent to SMS-based MFA, usually are not sufficient, since Lapsus$ has engaged in SIM-swapping assaults to realize entry to SMS MFA codes.
As Lapsus$ typically steals credentials by way of social engineering, Microsoft additionally beneficial rising worker consciousness about these sorts of assaults. Different strategies included making use of “trendy authentication choices” for VPNs, and making certain incident response communication channels are “carefully monitored for unauthorized attendees” in case Lapsus$ tries to sneak in.
As well as, Microsoft supplied a group of sources firms can use to assist with “detecting, searching, and responding to” assaults from Lapsus$ or teams mimicking the identical strategies.
[ad_2]
Source link









